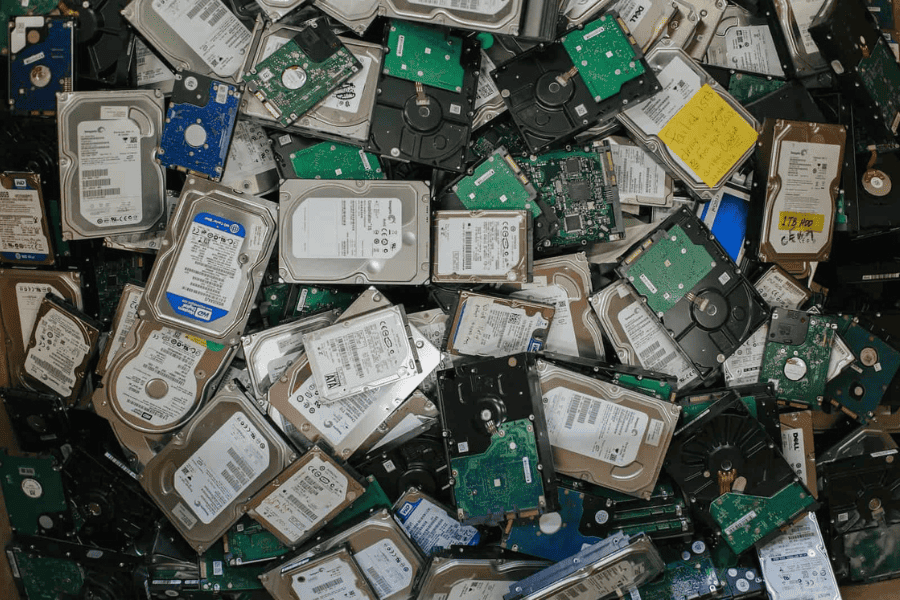
We protect data on the front end. We must protect it on the back end with the same diligence. Off-network IT equipment is, in fact, more prone to security breaches, simply because protecting sensitive information on retired assets isn’t always top of mind for busy companies. Additionally, retired IT assets can change hands multiple times in the disposal process and more points of contact mean an increased risk of data theft.
 The benefits of working with a trusted IT Asset Disposition (ITAD) vendor cannot be underestimated. A trusted vendor will prioritize your data security throughout the disposition process, maintain a secure chain of custody, and operate with third-party certifications such as R2. They also understand industry-specific regulations and work to maintain compliance in these areas. If you’re in the financial services industry, you can rest assured that a trusted ITAD vendor will have a working knowledge of these industry regulations:
The benefits of working with a trusted IT Asset Disposition (ITAD) vendor cannot be underestimated. A trusted vendor will prioritize your data security throughout the disposition process, maintain a secure chain of custody, and operate with third-party certifications such as R2. They also understand industry-specific regulations and work to maintain compliance in these areas. If you’re in the financial services industry, you can rest assured that a trusted ITAD vendor will have a working knowledge of these industry regulations:
FACTA: An integral part of the Fair and Accurate Credit Transaction Act (FACTA) is 2005’s Disposal Rule. This rule mandates that anyone in possession of consumer information must dispose of it in a proper manner. More specifically, any data that contains customer information must be erased or destroyed to such an extent that it cannot be reconstructed. Violating the Disposal Rule can result in hefty fines and lawsuits by affected parties.
SOX: The Sarbanes-Oxley Act (SOX) of 2002 requires that any publicly traded company must establish, document, test and maintain internal controls and data security procedures. It mandates strict auditing and financial regulations to protect shareholders, employees and the public. Part of this act addresses data destruction procedures and requires detailed auditing of the ITAD process in order to assure data security.
Want to learn more about developing an effective, secure and profitable ITAD disposition program for your business? Download our free guide here!
PCI DDS: The Payment Card Industry Data Security Standard (PCI DDS) pertains to organizations that accept credit cards as a form of payment. It requires these companies to maintain consistent data security standards throughout the asset lifecycle. During the disposition process, data must be thoroughly wiped or destroyed. These organizations must be able to prove in an audit that they are meeting the required data security standards.
GLBA: The Gramm-Leach-Bliley Data Protection Act (GLBA) of 1999 maintains a high data protection standard for financial institutions, all of which are privy to sensitive consumer information. The act requires a written financial security program and a contracted disposition vendor as well as a frequent reviewal of ITAD procedures. It specifies administrative, technical and physical provisions that help protect the privacy of sensitive financial information.
If it’s important to you to stay compliant with industry regulations regarding sensitive financial data, you can trust Tech Dump for your ITAD services. We have a working knowledge of financial industry regulations and maintain high standards for data security throughout the asset disposition process. Call us at (763) 432-3117 to learn more!
Recent News & Articles

Celebrating Juneteenth
Harnessing the Economic Potential of E-Waste Recycling: A New MN Study