No business is immune to cyber-attacks and the instance of these attacks is only increasing. In fact, since COVID-19, the FBI reports a 300% increase in cybercrimes. Fortunately, there are several ways you can ward off cyber-attacks and keep cybersecurity a top priority for your business.
Hot Tip #1: Know what you’re up against
Did you know that phishing attacks are the number one threat to your business’s cybersecurity? Phishing occurs when hackers imitate trusted companies or individuals in an attempt to gather sensitive data. If hackers are successful, they may require you to pay them a ransom to retrieve your data…a cost that many businesses simply can’t pay. Talk to your team members about phishing schemes so everyone can be on the lookout for these emails.
 Hot Tip #2: Password-protect your computer
Hot Tip #2: Password-protect your computer
Few things are easier than setting up a password on your computer. But not all passwords are created equal. Make sure you choose a smart password and make it something dramatically different from your passwords on other devices. And don’t save all of your passwords in an Excel doc. on your computer. That would be the motherlode for any hacker! One more thing to keep in mind: If you walk away from your computer, even briefly, always lock your screen. Sensitive information can be compromised in an instant.
Hot Tip #3: Designate a Chief Security Officer
It’s a wise idea to designate a security point person for your team. This person is in charge of all security training, and they are the one who calls the shots in the instance of a security breach. It’s helpful if this person is one of the higher-ranking employees in your company so they have experience and the authority to make critical decisions.
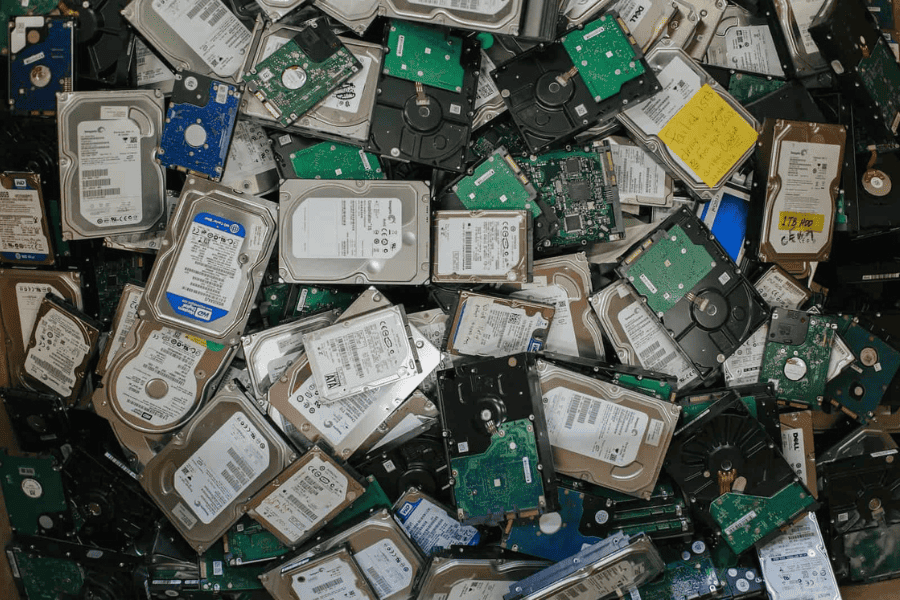
Hot Tip #4: Perform regular backups
In the unfortunate situation where you’re dealing with a ransomware attack, if all your data is backed up, you should not need to pay a ransom to retrieve it from the hackers. This alone could make the difference between your company surviving an attack and going belly up.
Hot Tip #5: Identify your critical assets
When you identify your most critical assets, you can take steps to protect them. It can also make it easier if you experience a cyber-attack to know how to navigate decisions regarding compromised data.
Want to learn more about developing an effective, secure and profitable ITAD disposition program for your business? Download our free guide here!
 Hot Tip #6: Install updates regularly
Hot Tip #6: Install updates regularly
In the same way that taking your vehicle to the dealership to address a recall helps protect your vehicle from future issues, installing recommended updates and patches helps gird up your software against cybersecurity threats. Hackers recognize and target weak points of entry so eliminating those with routine updates is a critical preventive strategy.
Hot Tip #7: Don’t share your devices with family and friends
Your family members and friends more than likely don’t have ill intent with your data, but they won’t be as vigilant as you are when it comes to protecting it or keeping an eye out for cybercriminal activity. As a best practice, reserve your device for business use only.
Hot Tip #8: Exercise caution with third-party suppliers
You work hard within your organization to keep your data secure. Do your suppliers? Don’t be afraid to ask suppliers about the cybersecurity rules they operate by. If they don’t have cybersecurity rules in place, be wary of working with them. Malware can spread from one device to another. Your business is the most secure when you’re working with other secure businesses.
Hot Tip #9: Get everyone involved
When it comes to cybersecurity, everyone can play. After all, it only takes one employee who is not vigilant or properly trained to compromise data and invite a cybersecurity attack that can take down an entire company. In fact, according to The Business Journals’ 2019 study, 59% of data breaches occur internally from a negligent employee or contractor and cost companies an average of $44k to repair! Hold regular training sessions and maintain open conversation about all of the ways each employee can contribute to data security.
 Hot Tip #10: Establish an ITAD plan with Tech Dump
Hot Tip #10: Establish an ITAD plan with Tech Dump
Hire Tech Dump to help you discard your retired IT assets. When you work with Tech Dump, you trust your sensitive data to a company that holds both NAID® AAA and Responsible Recycling (R2™) certification. Rest assured knowing that your data is handled through a secure chain of custody and by professionals with a working knowledge of industry regulations such as FACTA, SOX, PCI DSS and GLBA.
Want to learn more about how Tech Dump can help you protect your company’s sensitive data? Give us a call at (763) 432-3117!
Recent News & Articles

Earth Day at Repowered: 4 Ways We’re Making a Difference for the Planet

Celebrating Juneteenth